TL;DR
- Vercel confirmed a breach on April 19, 2026 tied to a compromised AI productivity tool called Context AI.
- An employee connected their Google Workspace to Context AI via OAuth. Context AI got breached first, and attackers used that to walk into Vercel.
- Once inside, the attacker read unencrypted environment variables (API keys, tokens, DB credentials) because Vercel's “sensitive” flag is opt-in, not the default.
- Data was listed on BreachForums for $2M. The attacker may have had 30+ days of undetected access.
- Vercel CEO confirmed the attacker was “likely significantly accelerated by AI.” Next.js and npm packages were audited and confirmed safe.
Vercel did not get hacked through a zero-day exploit or a sophisticated attack on their core infrastructure. They got hacked because one employee connected an AI productivity tool to their Google Workspace account.
That exact pattern exists inside your company right now.
Every OAuth-connected AI tool is a potential door. Most teams have dozens they have forgotten about.
On April 19, 2026, a threat actor posted on BreachForums claiming to have broken into Vercel's internal systems. The asking price was two million dollars, negotiable down to five hundred thousand in Bitcoin. The haul: API keys, NPM tokens, GitHub tokens, source code, database data, and roughly 580 employee records. Vercel confirmed the breach the same day.
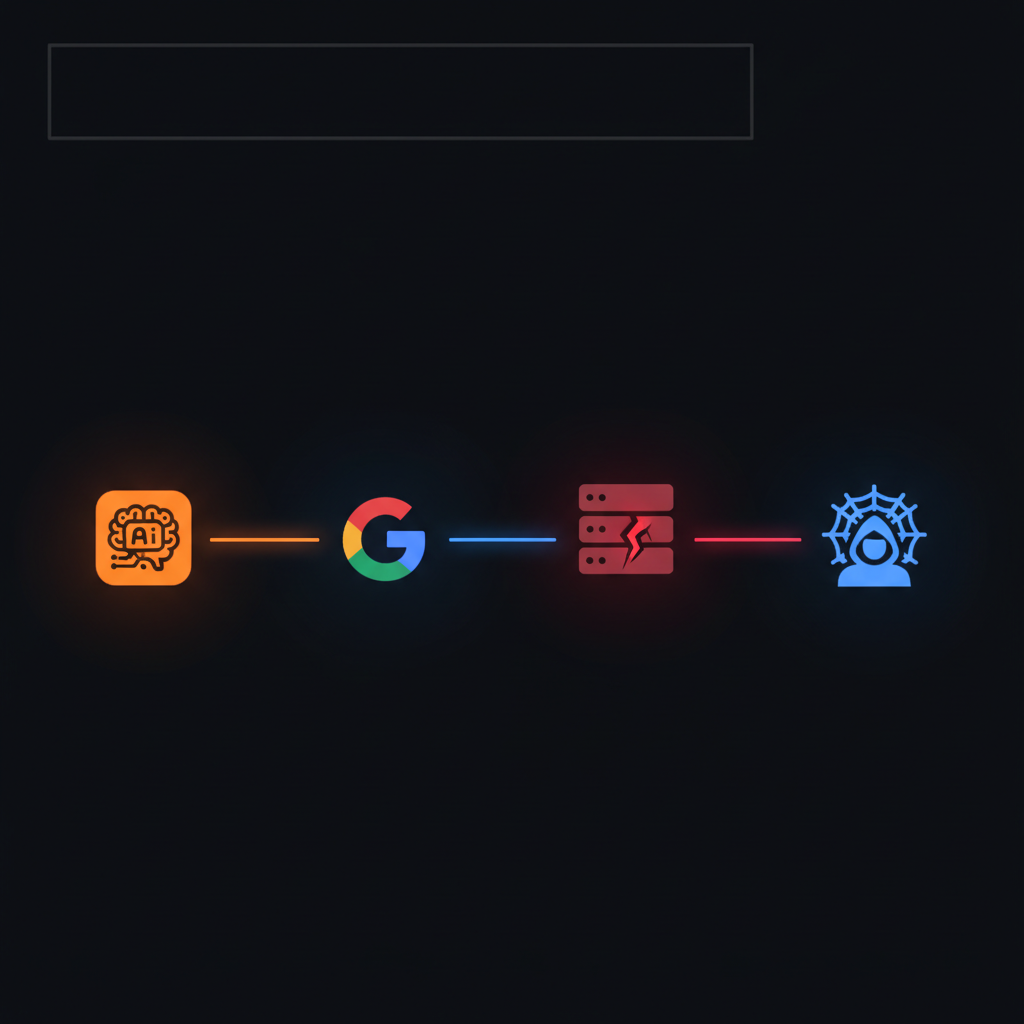
The attack path: one AI tool OAuth approval opened a chain that reached Vercel's internal systems. Vercel's official incident bulletin.
The Chain That Broke
How the attack unfolded
The attack did not start at Vercel. It started at Context AI, a third-party tool that helps teams build evaluations and automate workflows across their AI models.
A Vercel employee had connected their company Google Workspace account to Context AI via OAuth, a completely standard integration. You click “Approve,” the app gets the permissions it needs, and you move on. Nobody thinks twice about it.
Sometime in March, Context AI got breached. The attackers compromised OAuth tokens for a subset of users. Here is where Context AI made a decision that made everything worse: they quietly notified one customer and did not disclose the incident broadly. That silence gave the attacker a month-long runway.
By the time Vercel disclosed anything, the attacker had already used that hijacked OAuth token to take over the Vercel employee's Google Workspace account, pivot into Vercel's internal environments, and enumerate their way through unencrypted environment variables: database connection strings, third-party service credentials, API keys, authentication tokens.
They did not break any cryptography.
They just read what was already sitting there, unencrypted, because nobody marked it as sensitive.
Attack Chain
Context AI breached
OAuth tokens compromised, March 2026. No broad disclosure made.
Vercel employee's Google Workspace hijacked
Attacker inherits trusted session via stolen OAuth token
Pivot to Vercel internal systems
Session trust used to reach internal environments undetected
Environment variable enumeration
Unencrypted API keys, DB credentials, NPM tokens read
BreachForums listing
$2M ask, April 19, 2026. Breach discovered publicly, not internally.
The Design Flaw Nobody Was Talking About
Secure by default vs. secure by opt-in
Vercel's environment variable system has a feature called the “sensitive” designation. Mark a variable as sensitive and Vercel encrypts it so thoroughly that even their own internal systems cannot read it back. That is genuinely good security.

The sensitive flag is opt-in.
Not the default.
Variables without that flag are stored in a readable state internally, operating on an implicit assumption that any actor with internal system access is authorized. One hijacked OAuth session demolished that assumption entirely.
TL;DR on the env variable problem
If you use Vercel and have never explicitly marked your API keys, database URLs, and auth tokens as “sensitive” in the environment variable settings, those values were stored in a readable state. Any attacker with internal access could read them without breaking any encryption. Go mark them now.
Vercel CEO Guillermo Rauch confirmed it directly: the non-sensitive variable designation was the mechanism through which the attacker achieved escalation after initial access.
Security defaults matter more than security options. If the secure path requires deliberate action, most people will not take it, not because they are careless, but because they are moving fast and the system did not flag it as urgent.
Vercel has since shipped improved tooling. But every engineering organization running a similar pattern needs to hear this: secure by default beats secure by intention, every time.
Why This Was Not Just Vercel's Problem
The supply chain angle
Vercel is the primary steward of Next.js, the React framework with six million weekly downloads. They are the deployment platform behind thousands of enterprise, startup, and Web3 applications running simultaneously.
The attacker understood this. In the BreachForums post, they were explicit about the NPM token they claimed to have: “Send one update with a payload, and it will hit every developer on the planet who runs npm install.”
This was not a single company breach. It was a potential key to the global JavaScript supply chain.
If the NPM token was real and used, every developer running npm install next anywhere in the world would have been at risk.
Vercel audited Next.js, Turbopack, and all their open-source packages and confirmed they were not tampered with. The threat did not materialize. But the fact that a formal supply chain audit was required says everything about what was actually at stake.
The Part About AI Nobody Said Loudly Enough
AI-accelerated attackers are changing the threat model
Rauch's public statement included something most coverage treated as a footnote: he described the attacker as “highly sophisticated” and said they were “likely significantly accelerated by AI,” noting their “surprising velocity” and deep familiarity with Vercel's internal systems.
This matters more than the breach itself. If you are building with AI tools and deploying on cloud infrastructure, the people trying to get in are also using AI. The difference is they are using it offensively.
An AI-accelerated attacker compresses every phase of the kill chain. What took days now takes hours. What took hours now takes minutes.
Reconnaissance
Vulnerability Enumeration
Lateral Movement
The breach was not detected by Vercel's security team.
It was discovered because the attacker chose to monetize publicly. That gap (between when access was gained and when anyone knew) is the most important detail in this entire story.
TL;DR on AI-accelerated attacks
Your security team is operating on timelines designed for human-paced attackers. The attacker in this breach was not human-paced. AI tools compress reconnaissance, enumeration, and lateral movement into timeframes your incident response playbook was never built to handle. Update your assumptions.
What ShinyHunters Tells Us
Attribution, threat groups, and what is spreading
The BreachForums post claimed affiliation with ShinyHunters, a group linked to some of the most consequential breaches of recent years: Ticketmaster, Santander, AT&T, Rockstar Games. The actual ShinyHunters group denied involvement to BleepingComputer. The post may be a copycat, a splinter actor borrowing the name, or evidence of fragmentation within a larger network.
Attribution in modern breaches is unreliable. The more important signal: the tooling and tactics of serious threat groups are spreading to actors who never had to develop them independently. When you can buy a playbook, rent infrastructure, and use AI to accelerate execution, the barrier to running a ShinyHunters-style operation gets lower every year.
This connects directly to what the rise of agentic AI workflows means for security: the same automation that makes legitimate teams more productive is being applied to attack pipelines.
What You Need to Do Right Now
Immediate and longer-term actions
Rotate everything
API keys, environment variable tokens, any credential that touches a Vercel deployment. Treat all non-sensitive variables as potentially compromised.
Audit your OAuth connections
Go through every third-party app connected to your Google Workspace, GitHub, or internal tooling. Revoke anything without a clear, current business reason. The attack surface of most companies is 3x larger than they realize once they actually count OAuth integrations.
Mark your variables sensitive
In Vercel specifically: flag anything credentials-related as sensitive. The secure default should be your active choice, not the opt-in.
Review AI tool permissions with the same rigor as any vendor
Every AI productivity tool your team uses is now a security surface. Context AI did not build a malicious app. They built a useful one that got breached. The access you grant it is the access an attacker inherits.
Apply zero-trust to internal tooling
Enforce least-privilege access, short token lifetimes, and session verification at every internal boundary. Never assume an inherited session is trusted.
Hardware MFA on everything that touches infrastructure
Hardware security keys, not authenticator apps, for anyone with access to deployment systems. Authenticator apps can be phished. Physical keys cannot.
The Larger Pattern
This is not a one-off
Supply chain attacks are the dominant vector now because direct attacks on well-resourced companies are expensive and increasingly difficult. The perimeter of a company, the firewall, the access controls, the security team, is hardened. The perimeter of the third-party tools that company employees use is not.
Every AI integration, every productivity app, every OAuth connection is a door into your organization. Most of those doors are monitored by the vendor, not by you. Most of them were approved by someone who had no idea they were making a security decision.
If you want to understand why the way we build with AI is changing the risk landscape, this breach is the clearest example yet. The tools that make your team faster are the same tools attackers are targeting.
The Vercel hack was not a sophisticated exploit. It was an employee clicking “Approve” on a tool they found useful.
That is the new threat model. Act accordingly.
Related Reading
